Papermark GDPR Compliance in 2026: DPA, Sub-Processors, and EU Data Residency
Papermark's GDPR compliance explained: DPA, sub-processors, data residency, subject rights, and how we meet EU data protection requirements for VDR workflows.
Papermark is SOC 2 Type II compliant. The audit covers the AICPA Trust Services Criteria (security, availability, confidentiality) across our virtual data room, document sharing, and analytics platform. For the full security and compliance posture (encryption, hosting regions, certifications, sub-processors), see the Papermark security page.
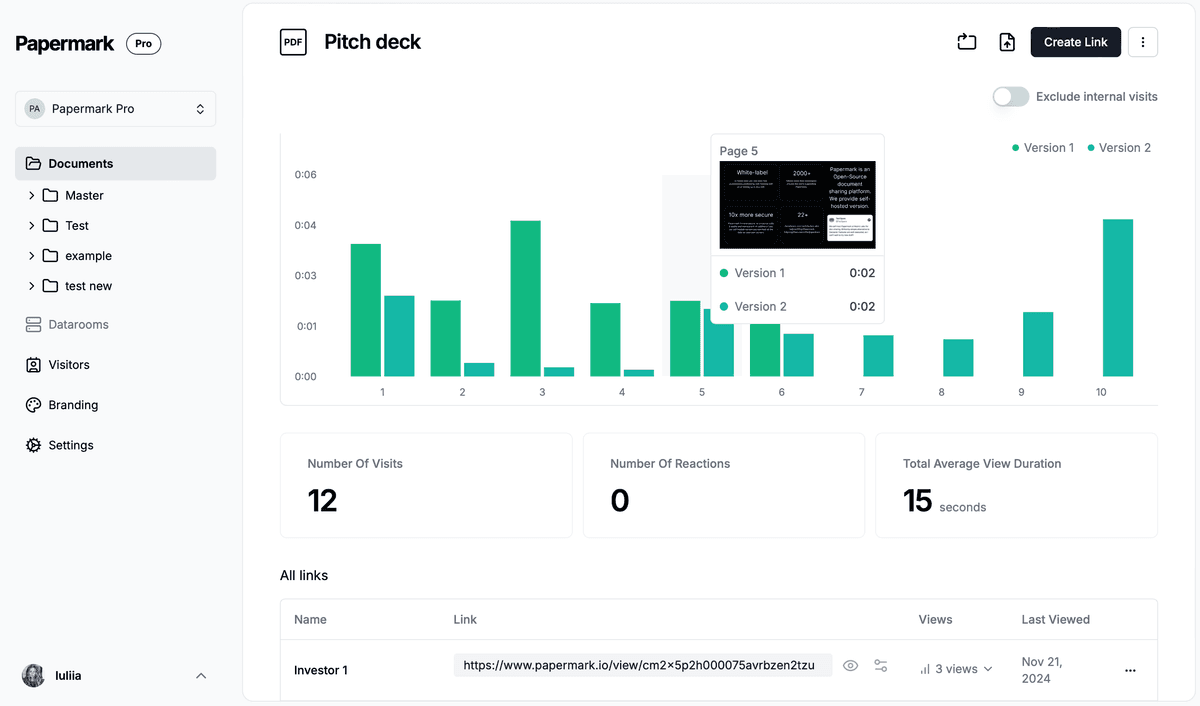
This guide explains what SOC 2 Type II means, what our audit covers, and why it matters for procurement teams assessing Papermark for M&A, fundraising, and regulated workflows.
SOC 2 (System and Organization Controls 2) is a rigorous auditing procedure developed by the American Institute of Certified Public Accountants (AICPA). It evaluates how service organizations handle customer data based on five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Type II reports evaluate the operating effectiveness of controls over a 6-12 month audit period, not just their design at a single point in time.
SOC 2 is the dominant security-and-controls attestation for B2B SaaS in North America and is increasingly expected in Europe and Asia-Pacific. For virtual data rooms handling M&A, fundraising, and regulated diligence, SOC 2 Type II is a baseline procurement requirement, not a differentiator.
SOC 2 audits are scoped around five AICPA Trust Services Criteria. Every SOC 2 audit includes Security (the Common Criteria); additional criteria are added based on the service organization's scope.
Security. Protection against unauthorized access, disclosure, alteration, and damage. Covers access controls, encryption, network security, incident response, and change management. Required in every SOC 2 audit.
Availability. System availability for operation and use as committed or agreed. Covers uptime, resilience, disaster recovery, and capacity planning.
Processing integrity. System processing is complete, valid, accurate, timely, and authorized. Relevant for systems performing calculations or automated processing (less central for a VDR).
Confidentiality. Information designated as confidential is protected. Covers data classification, access controls, retention, and secure disposal.
Privacy. Personal information is collected, used, retained, disclosed, and disposed of in accordance with AICPA Generally Accepted Privacy Principles (GAPP). Overlaps with GDPR but is a distinct framework.
Papermark's SOC 2 Type II audit covers Security (required Common Criteria) plus Availability and Confidentiality. Privacy is addressed through GDPR-aligned controls documented separately in our GDPR compliance overview.
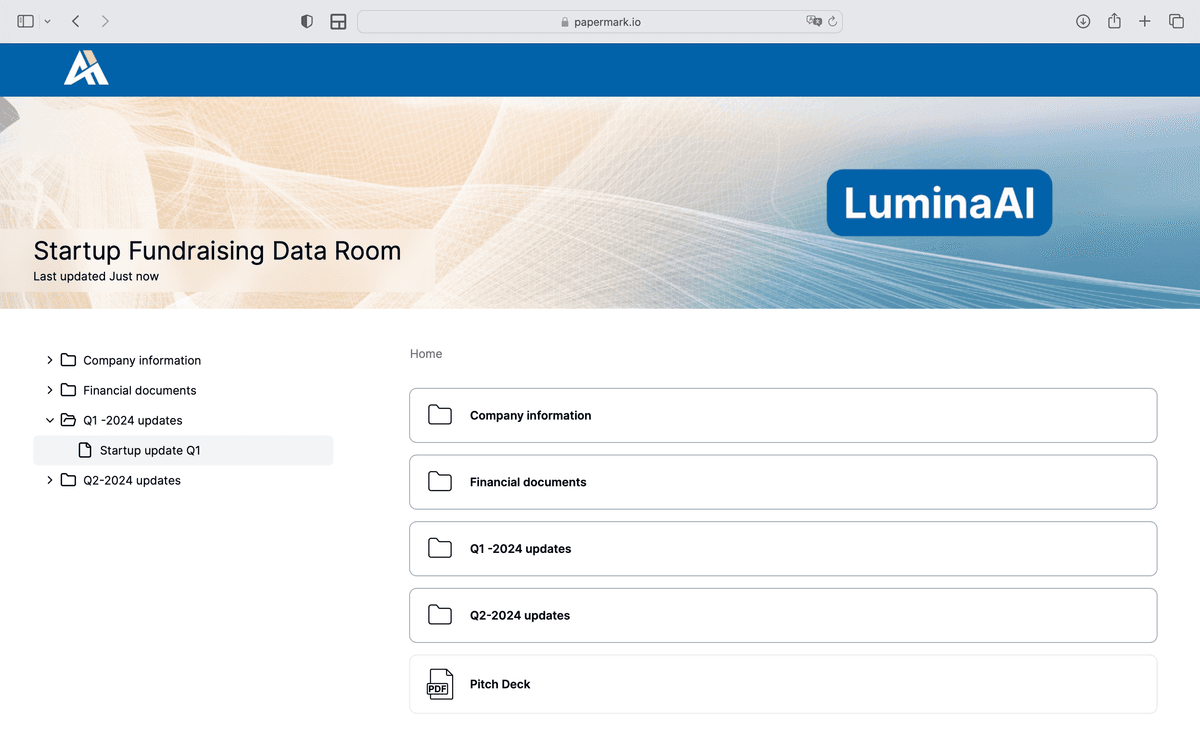
SOC 2 Type II is the single most common compliance attestation requested during VDR vendor assessments. Four specific workflows depend on it.
Regulated-industry procurement. Banks, healthcare, insurance, and government-adjacent organizations typically require SOC 2 Type II as a baseline before engaging any cloud vendor. Without it, the vendor fails the procurement screen.
Enterprise vendor due diligence. Large enterprises running vendor risk management processes routinely request the SOC 2 Type II report (under NDA) as part of onboarding. This is standard procurement hygiene, not a high bar.
M&A and fundraising data rooms. Institutional LPs and strategic acquirers increasingly ask what compliance attestations their target's VDR vendor holds. SOC 2 Type II is the answer that closes the conversation.
Post-incident liability. In the event of a security incident, having a current SOC 2 Type II report plus an ongoing monitoring program materially reduces liability and regulatory exposure compared to having no attestation.
A SOC 2 Type I report evaluates whether controls are suitably designed at a single point in time. A SOC 2 Type II report evaluates whether controls are suitably designed and operating effectively over a defined audit period (typically 6-12 months).
Type I is easier to achieve but weaker as an attestation: it confirms the controls exist, not that they work reliably over time. Type II is the industry-standard expectation for mature SaaS vendors handling sensitive customer data. Papermark is audited annually under SOC 2 Type II.
Compliance frameworks are not interchangeable. The table below maps the four most common frameworks for VDR procurement.
| Framework | Scope | Audit/Certification | Common in |
|---|---|---|---|
| SOC 2 Type II | AICPA Trust Services Criteria | Annual audit, report under NDA | US-centric, B2B SaaS |
| ISO 27001 | Information security management system | Formal certification by accredited body | EU and global enterprises |
| GDPR | EU personal data protection | Legal compliance, DPA, sub-processor list | Any processing of EU resident data |
| HIPAA | US healthcare PHI | BAA, compliance program (no formal cert) | Healthcare, biotech, medical devices |
Many enterprise customers request multiple frameworks. Papermark maintains SOC 2 Type II and GDPR alignment as standard, supports ISO 27001 via self-hosted deployment on customer infrastructure, and offers HIPAA readiness via self-hosted plus signed BAA on enterprise contracts.
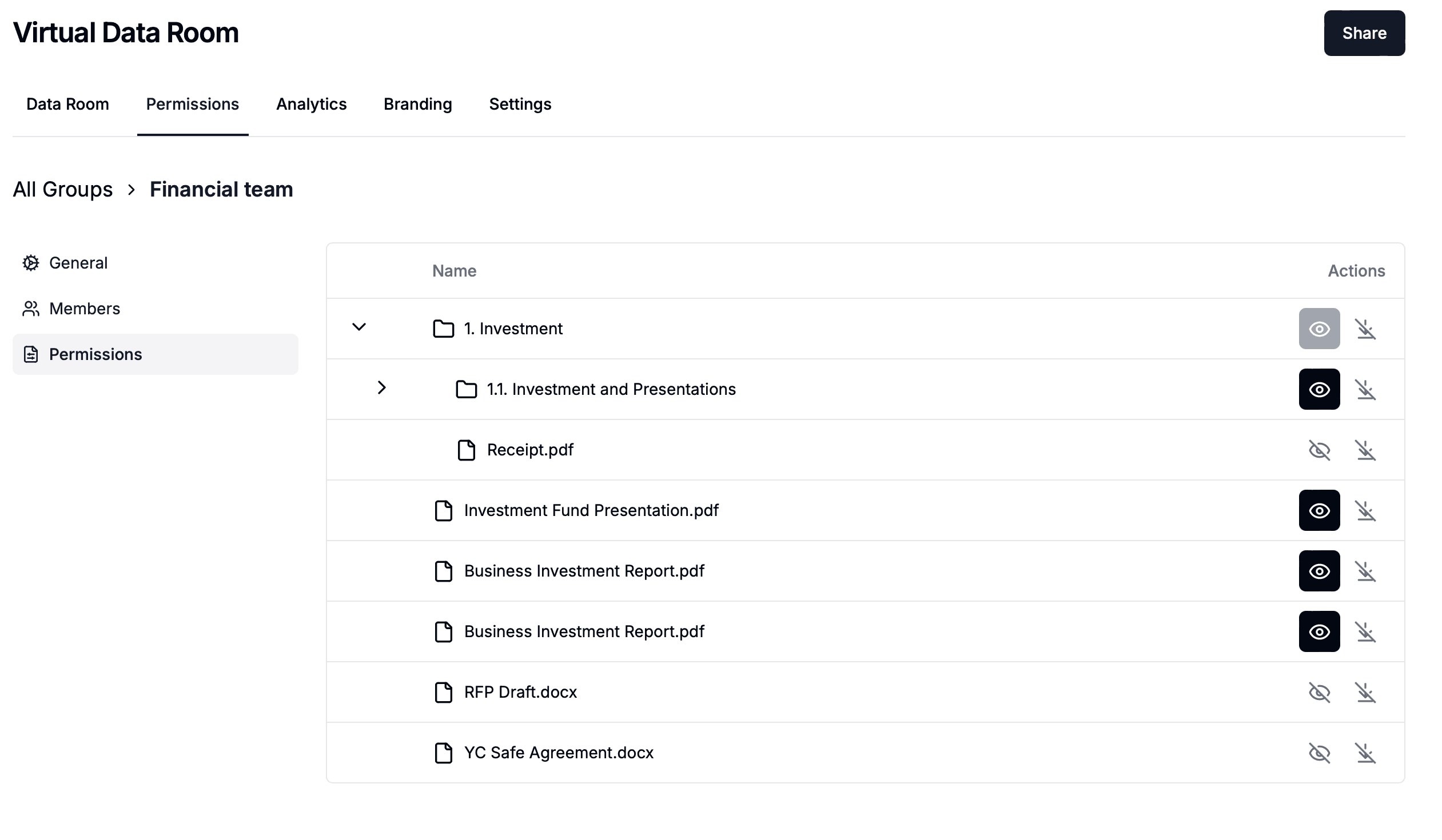
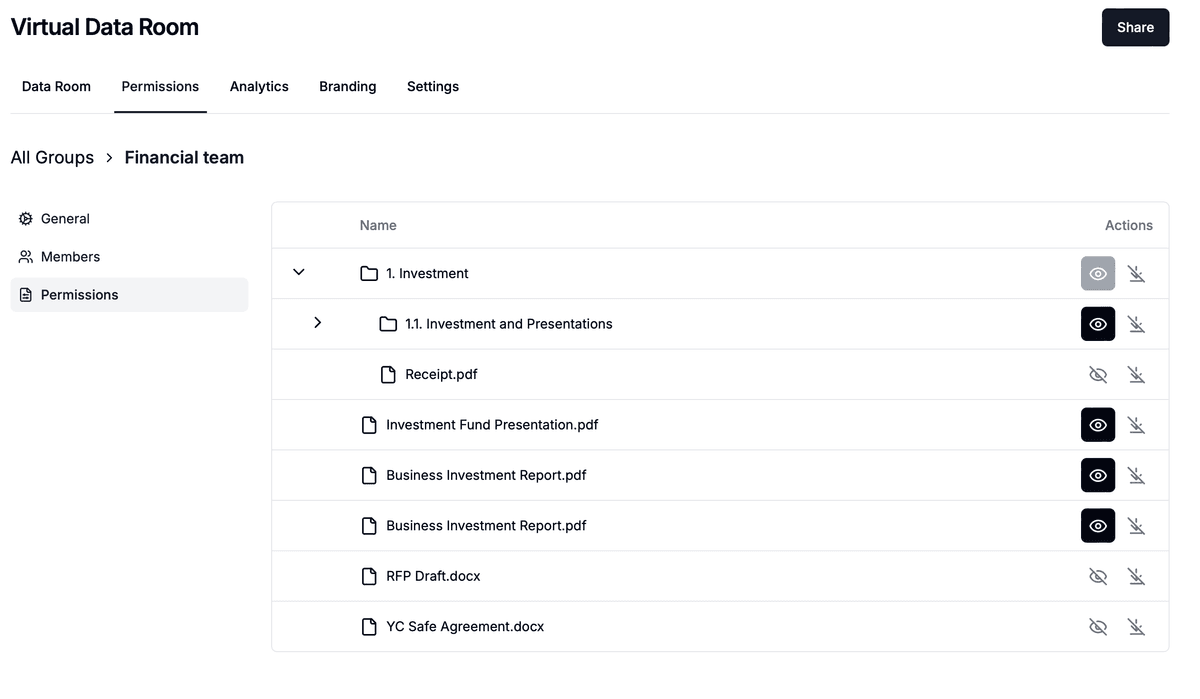
Append-only audit logging captures every view and download for the SOC 2 Confidentiality criterion:
Dynamic per-session watermarking marks every page with viewer email, IP, and timestamp:
For the live list of certifications, hosting regions, encryption standards, and the SOC 2 NDA request workflow, visit the Papermark security page.
Papermark's SOC 2 Type II report is available to enterprise customers and prospects under mutual NDA. To request the report:
The report includes the independent auditor's opinion, description of the system and its controls, results of tests of operating effectiveness, and management's assertion.
| Framework | Papermark status |
|---|---|
| SOC 2 Type II | ✔️ Audited annually |
| GDPR | ✔️ Compliant, DPA available |
| ISO 27001 | Via self-hosted deployment on customer infrastructure |
| HIPAA | Via self-hosted + signed BAA (enterprise plan) |
| CCPA | ✔️ Compliant |
| FDA 21 CFR Part 11 | Via self-hosted deployment with audit log export |
| Encryption at rest | AES-256 |
| Encryption in transit | TLS 1.3 |
| MFA | ✔️ |
| Self-hosted option | ✔️ (AGPL open-source) |